How to Protect Your Mobile Number from Continuous OTP/SMS Bombing
Are you annoyed by getting so many SMS/OTP within a few minutes? It's irritating while receiving it, as someone may be doing this willingly to prank you. The prankster may be using some application or website which shows OTP from different sites or merchandisers. Some messages also contain malware which can be dangerous for your device. In this article, we'll guide you through ways to stop SMS bombing on your phone.
What is SMS/OTP Bombing?
Most of us are aware of receiving SMS or OTP messages one at a time, but some applications and websites can bulk bombard such messages. SMS Bomber is a program that mimics the same messages several times and sends them to a particular phone number entered in the software. After receiving, a large number of SMS like that, the phone might lag or even crash sometimes.
Various online applications or apk files are present and known to the public, such as SMSBomber, BombItUp, Text Bomber, and others. These applications exploit vulnerable APIs (Application programming interfaces) owned by other companies, which send you the OTP messages.
How to stop SMS bombing on your iPhone/Android phone?
Method 1:
To stop SMS or OTP as someone has put your phone number on the tools which provide SMS flooding. You can visit specific websites that do SMS bombing services and register your number in DND (Do Not Disturb).
Here's the list of such popular tools:
ToolsOverFlow :
Step 1: Click on the link
Step 2: Enter your number in the large box below "Add your number to our blacklist"
Step 3: After typing your mobile number, confirm the captcha test by entering the sum of two digits given to you.
Step 4: Hit the Submit button (the red one), and you will stop receiving the SMS from now.
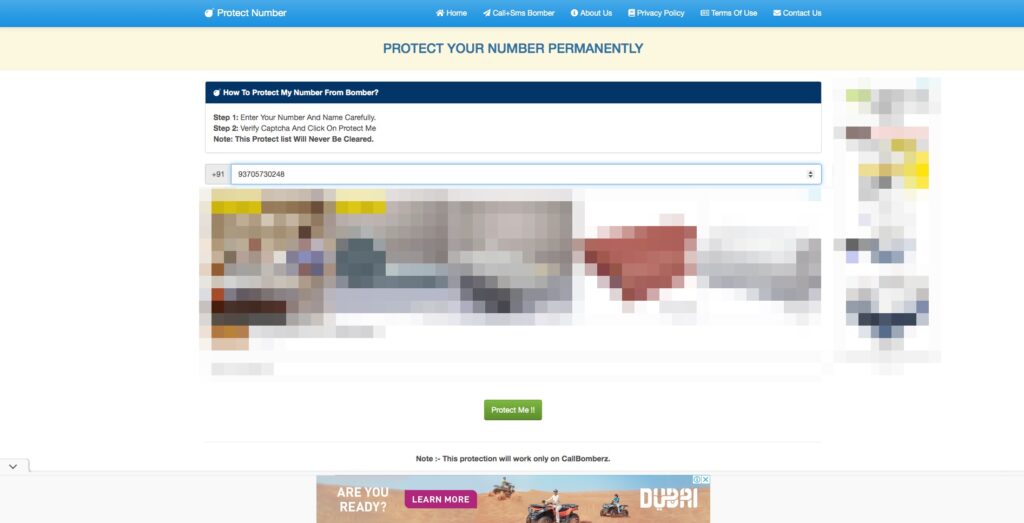
CallBomberz :
On this website, there is no need to enter your phone number to stop SMS bombing. You have to click on the link below, which will display a message showing that Call or SMS Bomber has now stopped.
Below are other links for different software where you can block SMS bombing on your phone number.
1. Mytoolstown
3. Callbomberz
Method 2:
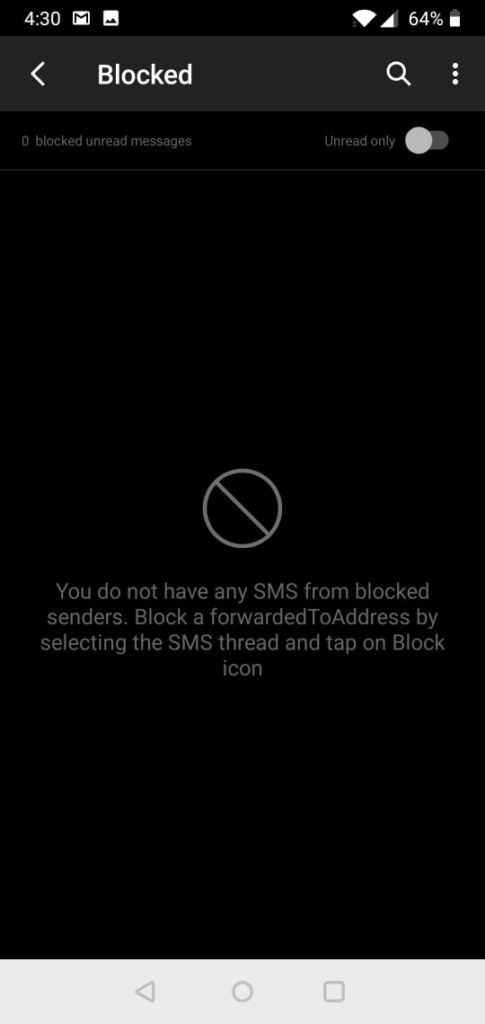
If you don't know the application or the apk file from which you are getting the SMS, then use this procedure to block SMS or OTP messages in your phone. As a precautionary measure, add your number to the protected list using the first method. If it doesn't stop then try out the steps outlined below.
For Android:
- First, open the messaging app on your phone.
- Press and hold on to the message you want to block.
- Tap on the Add to Blacklist button.
OR
1. Open the messaging app.
2. Go to the message or SMS you want to block.
3. Click on that SMS and press the two dots (or three dots, depending on the android phone you are using).
4. Hit the Add to Blacklist tab, and by doing that; you will remove the SMS from the list.
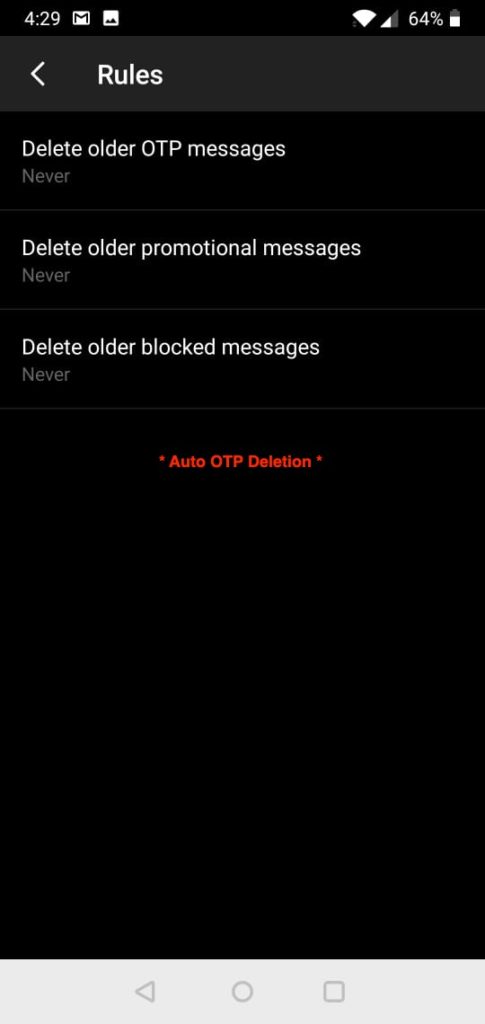
We recommend using the SMS organizer app for better management of SPAM messages.
For iPhone:
1. In the messaging app, open the SMS you want to block.
2. Click on the info button in the top right corner.
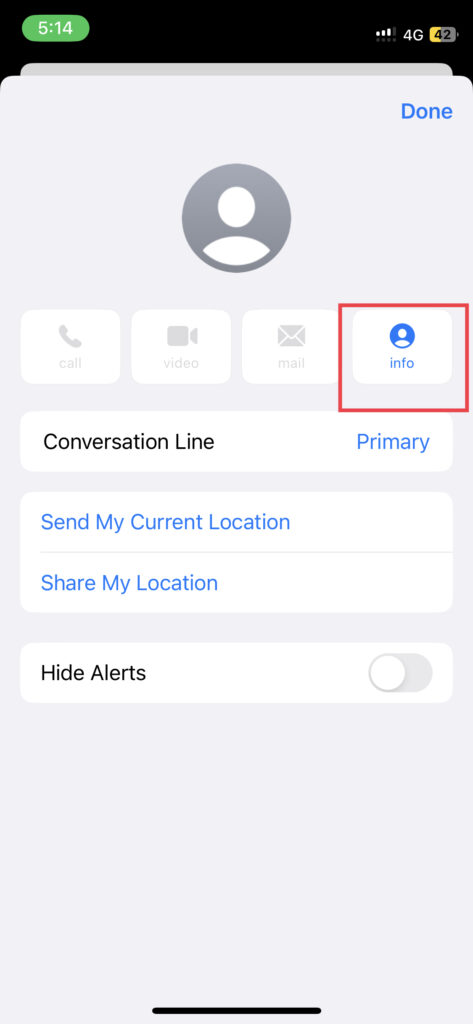
3. A new screen will pop up where you'll see the sender's contact details.
4. Then tap on the Block this caller, and a pop-up menu will appear at the bottom of the display.
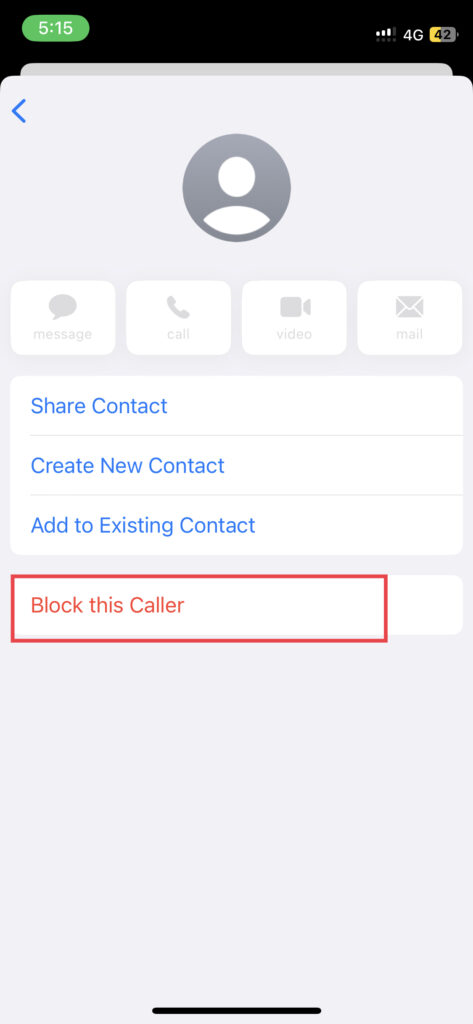
5. From that menu, hit the Block contact button to verify it.
If the above method is still not feasible due to a different SMS provider, then Android users can disable the notifications of SMS, and iPhone users can enable DND mode. Later when SMS bombing stops, you can delete those messages in bulk. You can also use the SMS organizer app to delete those messages.
Method 3:
Once the SMS bombing starts, put your phone on AIRPLANE mode for a specific time. If that also doesn't work, try to use a temporary mobile-specific BLOCKING technique, or you may use applications that block the SMS like Truecaller, RoboKiller, SMS Sheild, Spam blocker for android, and many more. Most of them are available for both iOS and Android.
How is SMS Bombing carried out?
As mentioned above, many companies apply an API program to transmit an OTP message to receivers. The purpose of the OTP messages may vary from user to user, as some get an OTP message to login into a specific domain, application some of us receive it when we forget our password. We often forget our passwords or log in to platforms, so the firms don't look into the security of these APIs. As a result, it's easy for people to find a way to get passed to those APIs.
For SMS bombing attacks, the attacker now uses their scripts to perform GET/POST requests on the APIs that send the OTP messages, and that demand automates message transmission and assists it in the SMS bombing.
How can Businesses safeguard against SMS bombing?
Due to poor implementation of web applications, many companies are burning their money because of SMS bombing. It's a loss for companies.
To avoid the loss of money, companies can implement the following ways to safeguard against SMS bombing:
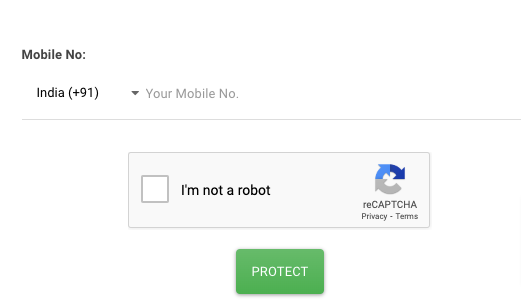
i. Captcha check ☑ in their OTP login page for human verification. Start using Cloudflare web spam protection. Cloudflare suggests installing a phishing-resistant security key or a TOTP (Time-Based One Time Password) software like Google Authenticator, or sometimes it gives us both. Google's ReCaptcha is another free alternative if you are not having a Cloudflare account.
ii. The other option is that the company must configure the daily max SMS sending limit in the database for every unique number. e.g. 15 or 20 SMS per day or some time interval between 2 SMS.
As you can see, Solution [i] is easy and very easy to implement from the business side.
Conclusion
To summarize, saving our phone numbers from continuous SMS bombarding can be tricky sometimes, but with the given solutions, you can reduce the damage. To decrease the frequency of SMS or OTP messages, one can install some SMS blocking apps or register their number to the Do Not Call Registry, which can save your phone from malware.
Users should also be wary of scams and phishing attempts, which can lead to a flood of unwanted calls and messages. By taking these proactive steps and remaining vigilant, mobile users can protect themselves from the annoyance and potential harm of continuous incoming bombarding. I hope this article has been helpful for you. Feel free to share your experience in the comments below.